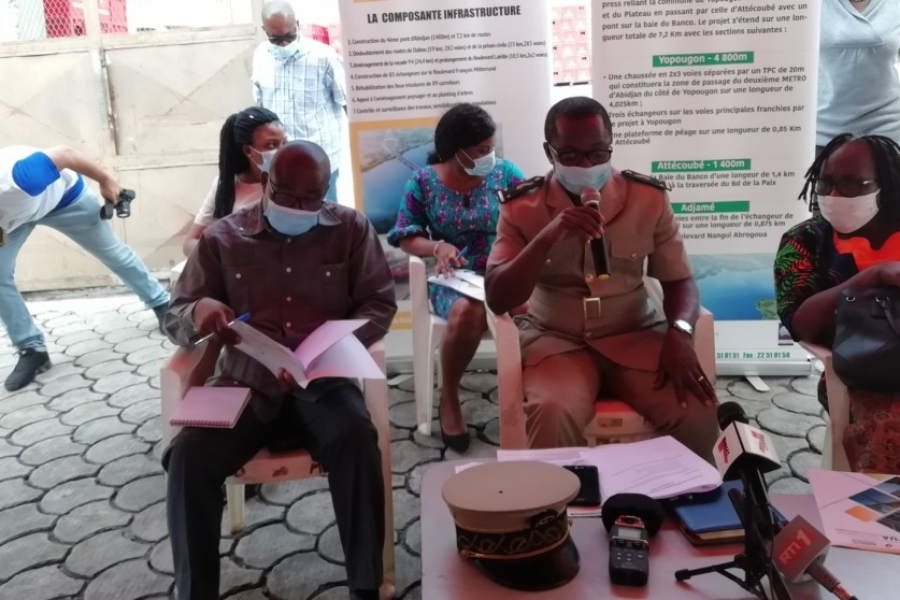
L’opération de libération de l’emprise de Bromakoté dans la commune d’Adjamé débutera le 08 juillet 2020 dans le cadre de la construction du 4ème pont.
En prélude à cette opération, le secrétaire général de la préfecture d’Abidjan André Martin Kacou, président du Plan d’action et de réinstallation a échangé avec les populations impactées par le projet en vue d’organiser leur départ dans de meilleures conditions et dans le calme. Au total 16 bâtiments ou immeubles seront démolis à partir du 08 juillet. Les personnes impactées au nombre de 143 dont 11 propriétaires non-résidents, trois propriétaires d’équipements, deux propriétaires d’activités commerciales, 42 locataires d’activités commerciales et 85 locataires sont concernés par ce départ.
Selon l’autorité préfectorale, les indemnisations ont été payées aux personnes impactées entre octobre et décembre 2019, soit déjà plus de six mois. «L’opération aura bien lieu le 08 juillet. Notre souhait, c’est qu’elle se passe dans la dignité, sans heurte et en toute sérénité », a souhaité M.Kacou signalant que 27 locataires n’avaient jusque-là pas négocié leur départ.
Des locataires ont plaidé pour le report de la date butoir pour leur permettre de chercher à se reloger et de permettre aux élèves de terminer leurs examens. D’autres ont estimé qu’ils n’ont pas encore été indemnisés. A la première préoccupation, l’autorité préfectorale a souligné que le projet est tenu par un calendrier.
Au regard de cette disposition, il a demandé à toutes les personnes impactées de libérer l’emprise avant le 08 juillet pour que le projet suit normalement son court normal. Concernant, les personnes qui n’ont pas encore été indemnisées, il a promis qu’elles auront leur forfait avant le début de l’opération.
Il a rassuré que cette opération de libération concerne que le site du viaduc dont les personnes ont déjà signé les documents et reçu leur pécule. Plusieurs sites sont impactés par le projet dont les quartiers de Yao Sehi, Doucouré et nouveau quartier à Yopougon, Fromager, Jean Paul 2, Boribana et Santé à Attécoubé et Bramacoté et Adjamé village dans la commune d’Adjamé.
Les personnes impactées par le projet sont des propriétaires résidents et non résidents, des locataires de maison, les protégés de propriétaires de maison, des commerçants, les employés d’entreprises qui exercent dans l’emprise du projet, etc. Le total des montants des indemnisations s’élèvent à 30 milliards de francs CFA pour plus de 14.000 personnes sont impactées par le projet.
AIP








 29_08_2025 à 16:08
29_08_2025 à 16:08 
 Rédaction
Rédaction 
 31
31